Hardware-Rooted Asset Identity for Ferrous Surfaces
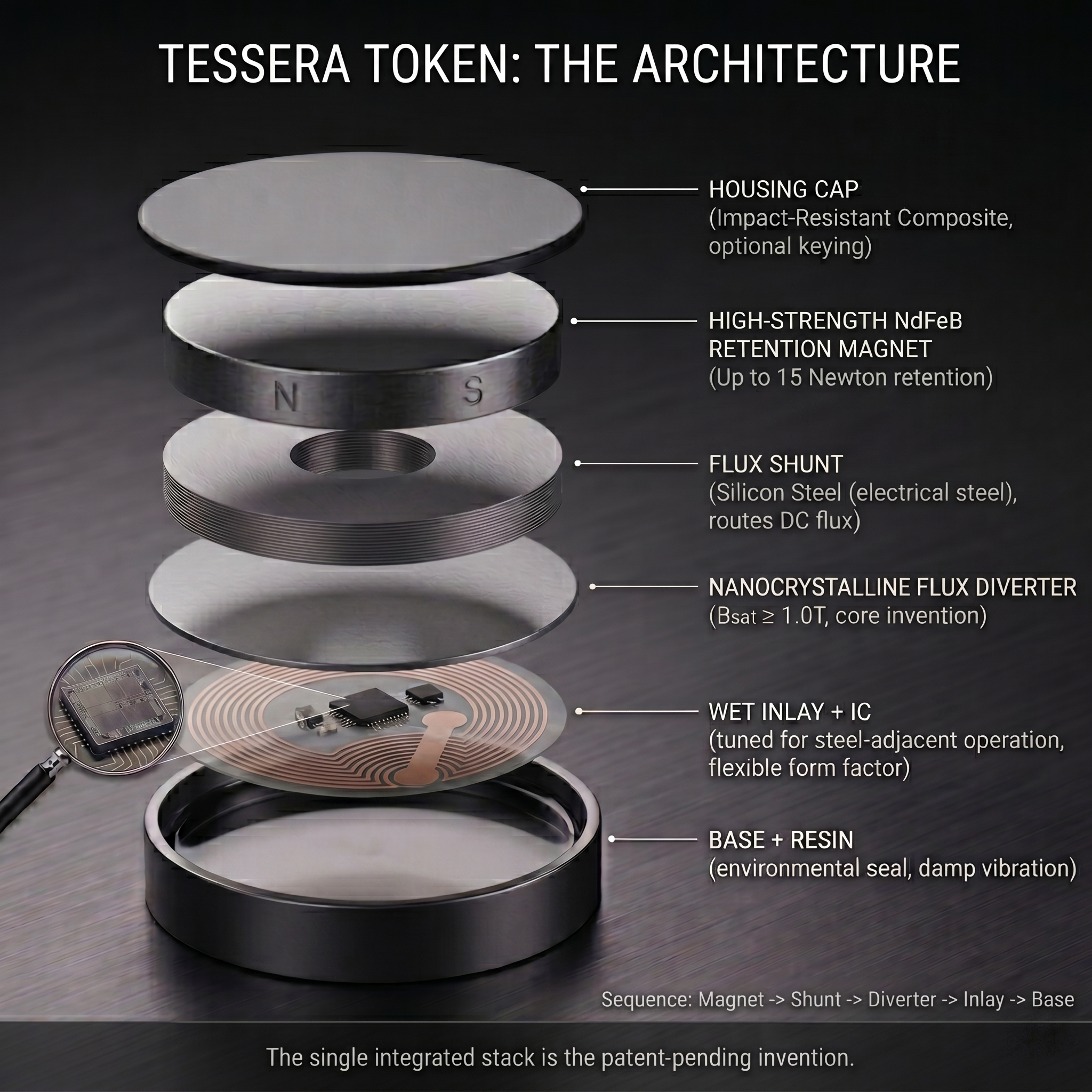
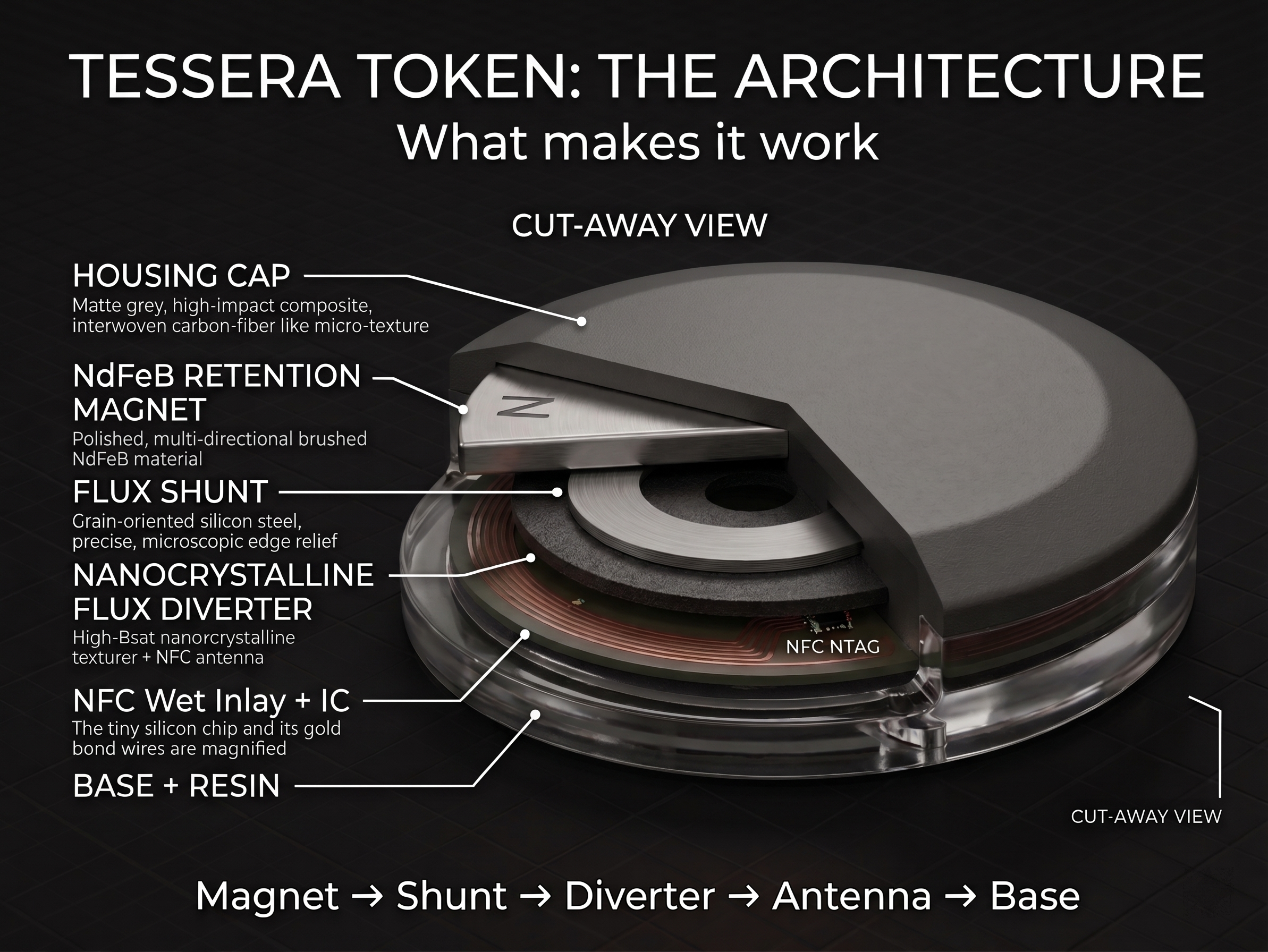
Tessera is a patent-pending passive NFC token that solves two problems simultaneously: it grips ferrous metal surfaces like a magnet, and it reads reliably despite the magnet — using a layered flux diverter stack that prevents the saturation failure mode that defeats every conventional on-metal tag. The Ordnance Series adds AES-128 cryptographic authentication and non-repudiable per-tap SUN verification, providing hardware-rooted asset identity that cannot be cloned, replayed, or passively spoofed.
Conventional Asset Identity Fails on Metal
Labels peel and fade. QR codes need line of sight and clean surfaces. Standard NFC tags detune when placed directly on steel — eddy currents kill the antenna. So-called "on-metal" tags use ferrite to manage this, which works until you add a strong magnet.
Strong Magnets Kill Ferrite-Based Tags
Put a high-strength neodymium magnet behind a ferrite-based on-metal tag and the ferrite saturates. Its permeability drops toward unity, the RF shielding collapses, the antenna detunes, and the tag stops communicating. The magnet that holds the tag to the steel is the thing that kills the tag. Conventional on-metal designs weren't built for this combination because nobody was trying to combine strong magnetic retention with HF communication — until now.
-
Housing + mechanical interlockImpact-resistant enclosure with optional keying feature that resists unintended removal while maintaining removable magnetic attachment. Interlock geometry is a design choice matched to the application threat model.
-
High-strength NdFeB retention magnetIndustrial neodymium iron boron magnet (N50–N52) providing 15+ Newton retention on ferrous surfaces. No drilling, no welding, no permanent adhesive. Removable by authorized personnel by overcoming magnetic attraction force — leaving evidence of removal attempts.
-
Flux shuntSteel layer that intercepts and routes peak DC flux from the magnet laterally, reducing magnetic pressure on the downstream flux diverter and keeping it further down the B-H curve for maximum RF permeability.
-
High-Bₓₐₜ nanocrystalline flux diverter + NFC antennaThe core invention. A soft magnetic material with saturation flux density ≥1.0 Tesla — compared to ~0.35T for conventional ferrite — remains magnetically permeable under the DC bias of the retention magnet, diverting static flux while simultaneously providing anti-metal RF shielding at 13.56 MHz. The antenna tunes and reads with the magnet engaged.
-
Wet Inlay + ICAntenna substrate tuned for steel-adjacent operation. IC selection is a design parameter — NTAG 215 for basic read/write (Forge Series), NTAG 424 DNA for AES-128 cryptographic authentication with CC EAL4 certified silicon (Ordnance Series). The flux diverter stack works with any ISO 14443-A compliant HF inlay.
-
Base + resinBottom cap and encapsulant that lock geometry, damp vibration, and provide environmental sealing for moisture, dust, and industrial fluid resistance.
The flux diverter is not new technology. The combination — high-saturation diverter, strong retention magnet, passive HF antenna, ferrous substrate, in a single integrated stack — is the patent-pending invention.
The same magnetic shielding stack supports both series. The IC selection and housing configuration vary by application. All variants share the core patent-pending architecture and are manufactured from the same process.
Consumer & Gaming
Passive HF NFC identity tokens for tabletop gaming, hobby collections, and consumer applications. Magnetically retained to metal game boards, terrain, and storage cases. Simple read/write for character data, scenario information, and collection management.
Industrial, LOTO & Defense
Hardware-rooted cryptographic asset identity for industrial equipment, LOTO programs, depot maintenance, supply chain integrity, and defense logistics. AES-128 SUN authentication with per-tap non-repudiable verification events. Anti-clone. Anti-replay. CC EAL4 certified IC. Optional mechanical interlock and TagTamper variants for elevated threat environments.
Every tap on a Tessera Ordnance Series token generates a cryptographically unique SUN (Secure Unique NFC) message. The message includes an encrypted UID, a tamper-evident read counter, and a MAC computed using the token's AES-128 key. The key never leaves the IC. The backend validates the SUN message. This is the difference between identity and authenticated identity.
| Property | Conventional On-Metal Tag | Tessera Forge Series | Tessera Ordnance Series |
|---|---|---|---|
| Magnetic retention on steel | No — adhesive or standoff only | Yes — NdFeB, 15+ N | Yes — NdFeB, 15+ N |
| Reads under magnet bias | No — ferrite saturates | Yes — flux diverter stack | Yes — flux diverter stack |
| Authentication model | UID only — static, clonable | UID only — static, clonable | AES-128 SUN — cryptographically unique per tap |
| Clone resistance | None | None | Hardware-rooted — AES key never leaves CC EAL4 certified IC |
| Replay resistance | None | None | SUN read counter — replayed transactions fail backend validation |
| Non-repudiation | None | None | Per-tap cryptographic verification — every event provably occurred |
| Tamper evidence | None | Physical evidence on removal | Physical evidence + optional TagTamper IC variant (permanent tamper state on unauthorized removal) |
| Mechanical tamper resistance | None | Optional interlock | Optional interlock — twist-lock, detent, or tool-required release matched to threat model |
| Power | Passive HF | Passive HF | Passive HF — no batteries, no maintenance |
| Backend model | Vendor SaaS — third-party ledger | Your Google or Microsoft tenant | Cryptographically verified SUN events to your Google or Microsoft tenant — non-repudiable, no vendor intermediary |
LOTO & Safety Compliance
Each LOTO inspection tap generates a SUN authentication event — timestamped, cryptographically signed, written to your EAM. The read counter flags gaps. A missed inspection shows up as an absence in the record, not a disputed paper log. The token on the breaker is passive; it powers up when tapped and goes dark when you walk away. No batteries to manage, no scanners to issue, no signatures to chase down.
Defense Depot & Maintenance
Hardware-rooted asset identity for vehicles, equipment, tools, and calibrated instruments in depot and field maintenance environments. Removes the adhesive and drill-hole limitations that prevent conventional RFID tagging on ferrous DoD assets. Compatible with existing NFC-capable mobile devices and reader infrastructure.
Supply Chain Integrity
Anti-clone authentication for ferrous containers, crates, and equipment throughout the defense supply chain. SUN authentication verifies at receiving that the tag installed at origin has not been substituted or cloned. Supports DoD supply chain integrity requirements where UID-only tags are insufficient.
Tool Control & Calibration Tracking
Authenticated identity for steel tooling in manufacturing, aerospace, and defense maintenance. Each tool tap generates a verifiable event — check-out, check-in, calibration touch — with a read counter that detects any tap not recorded in the system, regardless of whether the tool stayed on the correct asset.
Hardware-Rooted Non-Repudiation
The security property is anchored in EAL4-certified silicon. The AES-128 key is generated on-chip, stored in tamper-resistant hardware, and never transmitted. A valid SUN message is cryptographic proof the genuine IC was present — not a copy, not a replay, not a captured UID on a blank tag.
Passive — No Batteries, No Subscriptions
Power is harvested from the reader field during each tap. Dormant tokens consume nothing, fail nothing, and require no maintenance. Authentication events occur on demand, not continuously. No always-on radio. No subscription tracker. No battery replacement schedule.
Your Ledger, Your Rules
Every SUN authentication event goes directly into your Google or Microsoft tenant. No Aegidis intermediary. No NXP platform. Your audit trail lives where your other records live, managed by people who already have clearance to manage it. If you ever stop using Tessera, the data stays with you.
Layered Physical Security by Design
Threat model determines configuration. Base: magnetic retention (15+ N, deliberate removal effort required, physical evidence left). Add mechanical interlock for elevated environments. Add TagTamper IC variant for permanent tamper-state detection on unauthorized removal. The layers combine; the patent covers the combination.
Sample kits, pilot evaluations, and integration discussions for both the Forge Series and Ordnance Series are available for qualified buyers. Bring your use case — we'll tell you which configuration fits.